This Blog is created with a sole purpose of sharing knowledge and news about efficient softwares and latest technologies.Get insights and opinions about using complex but useful softwares.students can even look out for projects on this blog
Google search

Custom Search
Thursday, April 29, 2010
How to check for Unauthorized Activity on Your Email Account
Do you suspect that your email account is under attack? Do you want to maintain total security of your email account and make it 100% hack proof? Well, Some times our email account might have got hacked and we may not be aware of that. We may believe that our email account is safe, but in reality our private and confidential information may be falling into the hands of a third person.
Here are some signs of unauthorized activity on an email account.
1. Your new emails are marked as Read even if you’ve not read them.
2. Your emails are moved to Trash or even permanently deleted without your notice.
3. Your emails are being forwarded to a third party email address (check your settings->forwarding).
4. Your secondary email address is changed.
If you come across any of the above activities on your email account, then it is a clear indication that your email account is hacked.
Additional Security Features in Gmail to ensure the Safety of your Account
Gmail provides an additional security feature to protect your email account through the means of IP address logging. That is, Gmail records your IP address every time you login to your Gmail account. So, if a third party gets access to your account then even his/her IP is also recorded. To see a list of recorded IP address, scroll down to the bottom of your Gmail account and you’ll see something like this.
You can see from the above figure that Gmail shows the IP address of last login (last account activity). You can click on Details to see the IP address of your last 5 activities. If you find that the IP listed in the logs doesn’t belong to you, then you can suspect unauthorized activity.
Steps to be carried out to stop unauthorized activity on your email account
If you feel/suspect that your account is hacked then you must immediately take the actions mentioned below
1. Change your Password
2. Change your security question.
2. Remove any third party email address (if any) to which your account is set to forward emails.
3. Make sure that you can access the email account of your secondary email address.
4. Also change you secondary email password and security question.
This ensures that your account is safe from future attacks.
Please pass your comments and express your opinions.
How to Block Unwanted Emails
Do you want to block emails from your ex wife/husband, boyfriend/girlfriend? Do you want to block those annoying offers and newsletters that reach your inbox? Do you want to block those annoying messages from facebook and other social networking sites.Well here is a way to block all those unwanted and annoying emails that you do not want to see or read! With this trick you can block individual email address or the whole domain from which you do not want the emails to come from. Here are the step-by-step instructions to do this.
For Gmail
1. Login to your account
2. At the top-right corner, click on Settings
3. Under Settings, click on Filters
4. You’ll now see an option “Create a new filter“, click on it
5. Now in the From field enter the email address from which you do not want to receive the emails
For ex. you may enter john@gmail .com in the From field to block all incoming emails from this address. However if you want to block the whole domain then use the following syntax: *@xyz.com. Now all the incoming emails from the domain xyz.com will be blocked.
6. Click on Next Step, select the action you’d like to take on the blocked emails. You may select the option Delete it so that the blocked email is moved to trash. To unblock the email, all you need to do is just delete the filter that you’ve created.
For Yahoo
1. Login to your account
2. At the top-right corner, click on Options
3. A drop down menu appears, now click on More options
4. In the left panel select the option Filters and click on create or edit filters
5. Now click on Add
6. In the next screen, give a name to your filter and in the From header field enter the email address that you want to block.
Fox ex. john@gmail.com or if you want to block an entire domain then just enter @xyz.com. Dont enter *@xyz.com. Select the option Move the message to: Trash and click on Save Changes.
For Hotmail
1. Login to your account
2. At the top-right corner, click on Options
3. A drop down menu appears, now click on More options
4. Click on Safe and blocked senders link under Junk e-mail
5. Now click on Blocked senders
6. Type in the email address that you want to block under blocked e-mail address or domain field.
For ex. Enter john@yahoo.com to block the individual email address or just enter xyz.com to block the entire domain.
That’s it. You no longer receive those annoying emails in your inbox. Keep your inbox clean and tidy. I hope this post helps. pass your comments!
How to Test the Working of your Antivirus – EICAR Test
Have you ever wondered how to test your Antivirus software to ensure it’s proper working? Well here is a quick and easy way to test your antivirus. The process is called EICAR test which will work on any antivirus and was developed by European Institute of Computer Antivirus Research. This process can be used by people, companies and antivirus programmers to test the proper functioning of the antivirus/antimalware software without having to deal with the real computer virus which can cause damage to the computer. Here is a step-by-step procedure to test your antivirus.
1. Open a notepad (New Text Document.TXT) and copy the following code exactly onto it, and save the notepad.
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*
2. Rename the file from New Text Document.TXT to myfile.com
3. Now run the antivirus scan on this myfile.com file.
If the antivirus is functioning properly on your computer, then it should generate a warning and immediately delete the file upon scanning. Otherwise you may have to re-install your antivirus.
NOTE: Most antivirus will pop-out a warning message in the Step-1 itself.
You can also place the myfile.com file in a ZIP or RAR file and run a scan on it so as to ensure whether your antivirus can detect the test string in the compressed archive. Any antivirus when scanning this file will respond exactly as it will do for a genuine virus/malicious code. This test will cause no damage to your computer even though the antivirus will flag it as a malicious script. Hence it is the safest method to test the proper functioning of any antivirus.
1. Open a notepad (New Text Document.TXT) and copy the following code exactly onto it, and save the notepad.
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*
2. Rename the file from New Text Document.TXT to myfile.com
3. Now run the antivirus scan on this myfile.com file.
If the antivirus is functioning properly on your computer, then it should generate a warning and immediately delete the file upon scanning. Otherwise you may have to re-install your antivirus.
NOTE: Most antivirus will pop-out a warning message in the Step-1 itself.
You can also place the myfile.com file in a ZIP or RAR file and run a scan on it so as to ensure whether your antivirus can detect the test string in the compressed archive. Any antivirus when scanning this file will respond exactly as it will do for a genuine virus/malicious code. This test will cause no damage to your computer even though the antivirus will flag it as a malicious script. Hence it is the safest method to test the proper functioning of any antivirus.
Thursday, April 22, 2010
Changing ANY user's password without having to know the existing password
This tweak gives a user the opportunity to use it for good or bad. It enables the user to re-password any account
without having to know the existing password and also shows you every account that exists on the machine
(even the ones that are hidden). This is a good tool to use if you forgot a password to say your administrator account
and you needed to be logged into the admin account for any reason.
To view all of the user accounts:
1) While logged onto the computer, click on Start>Run>and type in CMD.
2) From the command prompt window, type in net users. This will show you every account that is made onto the computer
whether it is hidden or not.
To change an account password:
1) While logged onto the computer to an account that has administrative rights, click on Start>Run>and type in CMD.
2) Type in net user then the name of the account then * and press enter. heres an example: net user administrator * or
net user "mehra" * . Put the name in quotes if it contains spaces.
3) From there it should ask for a new password. Type in your new password (type very carefully - the command window won't display what you type) and once more to confirm it.
If you get the message that the command succeeded successfully you're all set!!
without having to know the existing password and also shows you every account that exists on the machine
(even the ones that are hidden). This is a good tool to use if you forgot a password to say your administrator account
and you needed to be logged into the admin account for any reason.
To view all of the user accounts:
1) While logged onto the computer, click on Start>Run>and type in CMD.
2) From the command prompt window, type in net users. This will show you every account that is made onto the computer
whether it is hidden or not.
To change an account password:
1) While logged onto the computer to an account that has administrative rights, click on Start>Run>and type in CMD.
2) Type in net user then the name of the account then * and press enter. heres an example: net user administrator * or
net user "mehra" * . Put the name in quotes if it contains spaces.
3) From there it should ask for a new password. Type in your new password (type very carefully - the command window won't display what you type) and once more to confirm it.
If you get the message that the command succeeded successfully you're all set!!
Monday, April 19, 2010
How to disable Recent Documents History
Normally when you open or access a document or file it is added to the list of recent documents on the Start Menu. This tweak will stop files from being added to the list.
1. Open your registry
2. Go to this location:
System Key: [HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\]
3. now click on edit >>new>>dword 32 bit
4.create a new dword
Value Name: NoRecentDocsHistory
Data Type: REG_DWORD (DWORD Value)
Value Data: (0 = disable restriction, 1 = enable restriction)
we will enter 1 to enable restrictions on recent document history
Exit your registry, you may need to restart for the changes to take effect.
1. Open your registry
2. Go to this location:
System Key: [HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\]
3. now click on edit >>new>>dword 32 bit
4.create a new dword
Value Name: NoRecentDocsHistory
Data Type: REG_DWORD (DWORD Value)
Value Data: (0 = disable restriction, 1 = enable restriction)
we will enter 1 to enable restrictions on recent document history
Exit your registry, you may need to restart for the changes to take effect.
Disable unnecessary services to free system resources
Services are programs that run when the computer starts up and continue to run as they aid the operating system in functionality. There are many services that load and are not needed which take up memory space and CPU time. Disabling these services will free up system resources which will speed up your overall computer experience. I recommend that you sort through the list and read the descriptions to decide if you need that service depending on what you want to do with your computer. Remember, you can always turn the service back on if you find that you need it in the future. Below is the procedure to turn off a service.
4.Once the services window has loaded we are ready to turn off unneeded services.
5. For instructional purposes we are going to turn off the DHCP client service.
6. select the service from the list of services running and right click on it
7. now click on the properties option
8.Once the properties windows has loaded locate the Start up type drop down box and select disable.
9.Then just click ok and the next time the computer starts the service will not be loaded.
you can see that DHCP CLIENT service has been stopped ,similarly you can disable all the unwanted services from the pool of services that are listed in the table mentioned above.
- Click the start button.
- Select run from the bottom of the right column.
- Then type services.msc in the box and click ok.
4.Once the services window has loaded we are ready to turn off unneeded services.
5. For instructional purposes we are going to turn off the DHCP client service.
6. select the service from the list of services running and right click on it
7. now click on the properties option
8.Once the properties windows has loaded locate the Start up type drop down box and select disable.
9.Then just click ok and the next time the computer starts the service will not be loaded.
you can see that DHCP CLIENT service has been stopped ,similarly you can disable all the unwanted services from the pool of services that are listed in the table mentioned above.
Friday, April 16, 2010
OpenDNS: Speed up your web browsing experience
When you type in a domain name such as http://techieassist.blogspot.com/ in your browser the computer must resolve the friendly name into an IP address of the server to download the web page and supporting files. Windows uses a DNS (domain name system) server to lookup this information. By default, Windows uses your ISP’s DNS server. Depending on your provider, the performance of their DNS resolving server varies. Some large national providers are known to provide unreliable and slow DNS servers.
The performance of the DNS server you are using is one component that affects the speed of your internet browsing. Since each domain name you type in must be resolved into an IP address, the amount of time that takes will delay the loading of any web page. Some users with overloaded ISP DNS servers can see delays in multiple seconds before web pages start to load.
OpenDNS provides free alternative DNS servers that anyone can use with any internet provider. Unlike many national internet providers, OpenDNS’s DNS servers are very fast and reliable. Using OpenDNS servers instead of your ISP servers will help you speed up your internet browsing by cutting down on the delay between resolving a domain name and getting the IP address so your browser can start loading the web page.
Configuring your computer to use OpenDNS servers instead of your ISP’s is a simple change that works in both Windows XP and Windows Vista:
The performance of the DNS server you are using is one component that affects the speed of your internet browsing. Since each domain name you type in must be resolved into an IP address, the amount of time that takes will delay the loading of any web page. Some users with overloaded ISP DNS servers can see delays in multiple seconds before web pages start to load.
OpenDNS provides free alternative DNS servers that anyone can use with any internet provider. Unlike many national internet providers, OpenDNS’s DNS servers are very fast and reliable. Using OpenDNS servers instead of your ISP servers will help you speed up your internet browsing by cutting down on the delay between resolving a domain name and getting the IP address so your browser can start loading the web page.
Configuring your computer to use OpenDNS servers instead of your ISP’s is a simple change that works in both Windows XP and Windows Vista:
- Click on the Start Button and type in ncpa.cpl and hit Enter. In Windows XP Click on the Start Button, click Run and then type in ncpa.cpl
- Right click on your active network connection that you use to connect to the Internet and select Properties.
- On the Networking / General tab, select Internet Protocol (TCP/IP) (version 4 on Windows Vista & 7) and hit Properties.
- On the properties screen, select Use the following DNS server addresses and then type in 208.67.222.222 in the preferred and 208.67.220.220 in the alternate boxes.
- Hit OK twice and you are finished.
Tweaking XP: To Speed Up Your Internet Access
Tweaking your Internet connection for speed
Almost every computer user has different Internet connection conditions. Some users have very high-speed connections, while others have slow connections. Some users have high-speed connections using cable-based technologies, while others have high-speed connection through DSL-based technologies. On top of these differences, some are located farther away from their local network switching station than others and have a higher latency (delay) on their connections because of the distance the data has to travel. All of these different connection conditions make every user unique.
The TCP/IP protocol settings can be optimized for best speed under each of these situations. By default, Windows XP has these settings set in a "one size fits all" approach. As I mentioned earlier, Windows has to be abstract in certain areas because of its broad user base. Because of this approach, many users can fine-tune their settings to be optimal for their connection conditions. Doing so will optimize the data transferred so your network connection will be more efficient, leading to high speeds.
With a little help from some fine online tools and software programs, you can test your Internet connection and decide what needs fine-tuning. The process of tweaking your Internet connection is not always easy, but it is doable.
Caution: Before going any further, you are strongly advised to create a system restore point, so that if things go wrong, which is not very likely, you will have a backup.
The next step in the tweaking process is to get all of the software that is needed. The main software program that you will use is called CableNut, which is developed by CableNut Software and is available for free at www.cablenut.com. CableNut is a great program that allows users to edit their Internet settings easily. Visit their Web page and download and install the latest copy.
Calculating settings for CableNut
Once you have downloaded CableNut, you are ready to start getting information to use with the program. The first value that you will need to calculate is the latency of your connection when it is active. To do this, you will use the trace route command built into Windows XP. Follow these steps to get the latency value to use for your connection:
- First, open up a Command Prompt window. This can be done by clicking the Start Menu and selecting Run. Then type cmd in the text box and click the OK button.
- Once Command Prompt is loaded, you are ready for the next part. Because you will need to test your connection when it is active, you will need to find something large to download that will run the duration of the test, which will be approximately 30 seconds. I recommend that you head over to www.microsoft.com/downloads and find some huge file, such as the .NET SDK framework, which is over 100,000 KBs. For the test, you want a file big enough so it will be downloading throughout the whole test. Those of you on a dialup connection can pick a much smaller file than those on a high-speed connection.
- Once you have your download test file picked out, start the download and switch back to the Command Prompt window. In that window, type tracert www.tweakxp.com. During the test, you will see many times displayed in milliseconds. After the test finishes, pick the highest time, as shown in Figure 11-12. This is the number that you will use as your latency. Also, feel free to cancel the download after the test is finished.
Entering the latency value into CableNut
Now that you have the latency value calculated, you are ready to enter this information into a great online CableNut settings calculator written by Joe Zeiler. Open up your Web browser and visit www.j79zlr.com/cablenutXP2k.php (the URL is case-sensitive!), then follow these steps to get the values to enter into CableNut:
- Once you have opened up the site, the first part of using the settings calculator is to select your connection type from the drop-down box.
- Next, you will have to do a little research and find out exactly what your upload and download speeds should be for your Internet connection. I had to contact Comcast, my ISP, to find out the exact values, because the values are not always advertised. Once, you get those values, make sure that they are in kilobits per second and not kilobytes per second (KB= kilobytes; Kb= kilobits), then enter them in the corresponding text boxes on the Web page.
- Enter the latency value that you calculated earlier into the latency text box on the Web page and then click the Calculate button.
- After you hit the Compute Settings button, scroll down and you will see the values that were calculated. Now, you are almost done. Continue scrolling down until you see a button labeled CCS File Generator under the Cablenut setting files section. Click that button and a new window will pop up with some text in it. Make sure that you have any pop-up blockers disabled when you are using the calculator.
- Use the mouse and select all of the text and numbers that are displayed in the pop-up window. Right-click the mouse and select copy to copy all of the text on the page to the clipboard.
- Now open up Notepad from the Accessories folder. In the blank Notepad window, paste the contents of the clipboard by right-clicking the white background and selecting Paste.
- Once Notepad is displaying the information that you copied from the pop-up window, all that is left is to save the file in the CableNut format. To do this, click the File menu bar item and select Save As. Then in the Save As Type drop-down box, select All Files. Key in myCableNutSettings.ccs in the file name text box. Specify the Save location, such as the desktop, and click the Save button.
You are now finished with the calculations that will optimize your Internet connection. That wasn't too hard now, was it?
Using CableNut to adjust settings
Now that you have created your CableNut settings file, or will be using the 56K settings file, you are ready to start using CableNut. Follow these steps to import the new optimized settings into your system:
- Start up the CableNut application by opening the Start Menu and browsing to the CableNut folder and selecting the adjuster application.
- When CableNut has loaded, click the File menu bar item and select Open Custom Settings File. Navigate to where you saved your settings file, or if you are a 56K user, use the file that is on the companion CD, called 56K_CableNut.ccs, and then click the Open button.
- Now you will see the information boxes for all of the different parameters filled with your connection-specific information, as shown in Figure 11-13. The last step is to click the Save to Registry button and you are finished. After you click the Save button, reboot, and your new settings will be in effect.
Caution:
According to www.j79zlr.com/cablenutXP2k.php, some of the CableNut settings can cause problems for a small amount of DSL customers. If you are experiencing network problems after optimizing your connection, use System Restore to revert to your last restore point. You may try the settings again, but blank out the MaxNormLookupMemory, MaxFreeTcbs, MaxHashTableSize, and FastSendDatagramThreshhold fields before applying. If you continue to have problems, or if you have problems with the directions and still want to optimize your connection, a great forum to get help on this topic is at www.broadbandnuts.com,
According to www.j79zlr.com/cablenutXP2k.php, some of the CableNut settings can cause problems for a small amount of DSL customers. If you are experiencing network problems after optimizing your connection, use System Restore to revert to your last restore point. You may try the settings again, but blank out the MaxNormLookupMemory, MaxFreeTcbs, MaxHashTableSize, and FastSendDatagramThreshhold fields before applying. If you continue to have problems, or if you have problems with the directions and still want to optimize your connection, a great forum to get help on this topic is at www.broadbandnuts.com,
Tweaking XP: To Speed Up Your Network
This excerpt is from a book, Hacking Windows XP, shows you how to tweak the Windows XP System Registry settings to improve network and Internet speed.
The speed of your network connection doesn't just depend on the speed of your hardware. Windows is an operating system that is designed to work on a variety of different hardware and network setups. Because of the abstract nature of the operating system, it cannot be optimized for user-specific hardware setups.
Depending on the type of network connection you have, you might be able to tweak your connection so that the speed of your Internet, as well as your local area network, will be faster. By hacking the System Registry and editing the TCP/IP parameters, you can fine-tune the values to take advantage of more reliable, faster Internet connections, such as DSL and cable.
These next sections will guide you through the steps of increasing both the speed of your local area network and your Internet connection.
Does your computer slow down when you browse your local area network and connect to other computers that are sharing data? One of the most common causes of this slowdown is a feature of Windows Explorer that looks for scheduled tasks on remote computers. This effort can take some time on some computers and can really slow down your browsing. The window with which you are browsing the network may appear to freeze momentarily, as the system is waiting for a response from the remote computer.
Although this problem is a complex one, the solution is very simple. Instead of having to wait for the remote scheduled tasks, which is useless information to anyone who is not a system administrator remotely configuring scheduled tasks, you can disable this feature.
In order to do this, you will have to hack the System Registry and delete a reference to a key so that this feature will not be loaded. To do this,
follow these steps:
follow these steps:
- Open up the Registry Editor by clicking the Start Menu and selecting Run. Then type regedit in the text box and click the OK button.
- Once the Registry Editor has loaded, expand the HKEY_LOCAL_MACHINE key.
- Next, expand Software and then Microsoft.
- Locate Windows and expand that as well.
- You will want to be editing the main system files, so expand CurrentVersion.
- Because this feature is a feature of the Windows component known as Explorer, expand the Explorer key.
- Next, you will want to modify the remote computer settings, so expand the RemoteComputer key and then expand the NameSpace key to show all of the features that are enabled when you browse to a remote computer.
- In the NameSpace folder you will find two entries. One is "{2227A280-3AEA-1069-A2DE-08002B30309D}" which tells Explorer to show printers shared on the remote machine. The other, "{D6277990-4C6A-11CF-8D87-00AA0060F5BF}," tells Explorer to show remote scheduled tasks. This is the one that you should delete. This can be done by right-clicking the name of the key and selecting Delete.
Tip:
If you have no use for viewing remote shared printers and are really only interested in shared files, consider deleting the printers key, "{2227A280-3AEA-1069-A2DE-08002B30309D}", as well. This will also boost your browsing speed.
Once you have deleted the key, you just need to restart and the changes will be in effect. Now your network computer browsing will be without needless delays
Disabling unneeded protocols
With every computer comes programs installed that you do not need. As with extra programs taking up space, extra protocols are just wasting your network connection and can actually slow it down. How is this possible? By default, a few different protocols are installed on your computer to allow for maximum compatibility with other computers on a network; these protocols each require bandwidth to operate. Most users will not use too many protocols, and their computers will use up a portion of their connection as they respond and transmit information for these protocols.
Additionally, with extra protocols installed on your network adapter connected to the Internet, you increase your risk of security-related problems. One of the most common risks for broadband users is that they have the Client for Microsoft Networks networking protocol enabled on their connection. This protocol allows everyone in their neighborhood to connect to the users' computers and view any files that they may be sharing. This fact alone should be a good enough reason for you to turn off the extra protocols. But with them disabled, you will also save a little bandwidth as well.
Viewing protocols on your network adapters
Viewing the protocols installed and active on your various network adapters is easy. Just follow these quick steps and you will be viewing them in no time:
Viewing the protocols installed and active on your various network adapters is easy. Just follow these quick steps and you will be viewing them in no time:
- Right-click the My Network Places icon on the desktop or in the Start Menu and select Properties. If the My Network Places icon is not in either of those locations, then go to the Control Panel and click the Network Connections icon that is shown under the Classic view.
- Next, right-click the network adapter with which you want to view the network protocols and select Properties.
- This will bring up a list of the protocols installed as well as active on your adapter, as Figure 11-11 shows. The protocols that are installed but not active are indicated by the absence of a check in the checkbox.
Disabling a specific protocol
Now that you have the list of installed and active protocols on your screen, you are ready to disable a protocol. To do so, just click the check box to remove the check. Then click the OK button and the protocol is no longer active on the network adapter.
I highly recommend that you disable all protocols except for the TCP/IP protocol (also referred to as the Internet Protocol). Doing so will optimize your adapter for speed and security.
Be aware that if you remove the Client for Microsoft Networks protocol and the file-sharing protocol, you will no longer be able to share your files. Additionally, you will no longer be able to connect to remote computers to view their shared files.
Also keep in mind that if you have multiple adapters in your machines, such as a wireless adapter, a wired network adapter, and a dialup modem, you will have to repeat the preceding instructions for each adapter.
3ways of downloading YOU TUBE videos : 3rd using softwares
Software Programs to download Youtube videos
The following list contains software programs for all popular operating systems that allow a user to download videos from Youtube.
1. TubeQueue (Windows):
TubeQueue: A program for the Windows operating system that can queue, convert and download multiple Youtube videos. The program comes with its own search interface making it completely independent from the Youtube website.
2. Free FLV Converter (Windows):
Free FLV Converter: A software program that can search for, download and convert Youtube videos and videos from other web services. It’s biggest strength is the search that can easily handle thousands of results providing comfortable options to download multiple videos at once from Youtube.
3. Orbit Downloader (Windows) : Orbit is a very popular download manager that supports a variety of popular media sites out of the box including Youtube, MySpace or Pandora. It integrates with web browsers and comes with the Grab++ module that can be used to catch and download media files.
Orbit Downloader
4. Youtube-DL (Linux, Windows): A command line program to download videos from Youtube
Youtube-DL
5. Abby and CCLive (Linux): Abby is a frontend for CCLive that can be used to download videos from various popular video hosting websites including Youtube.
Abby and CClive
6. GetTube (Mac): An application for Apple Mac computers that can be used to download Youtube videos.
GetTube
There are literally dozens of other applications, web services and browser plugins that can be used to download videos from Youtube. Please leave a comment if you think we should add another free services, plugin or software to the list.
3ways of downloading YOU TUBE videos : 2nd using Web browser plugins
Web Browser Add-ons to download Youtube videos
The following list contains ten web browser add-ons and plugins for popular web browsers such as Mozilla Firefox or Internet Explorer that allow users to directly download videos from video portals like Youtube. These add-ons have the advantage that the videos can be downloaded directly without having to visit another website to do so.
1. Video Download Helper (Firefox): One of the most popular Firefox add-ons. It supports many different video portals including Youtube. The add-on will change its icon in the status bar whenever a website with media links is visited.
2. NetVideoHunter (Firefox):
NetVideoHunter: Will recognize Youtube videos and add them to its queue with the possibility to download the videos immediately or at a later time. Videos can also be played in the interface as well.
3. Viloader (Firefox, Internet Explorer, Opera): A plugin that installs itself in three different web browsers. It offers a download video right-click context menu option that can be used to download the videos from Youtube and other video portals.
Viloader
The following list contains ten web browser add-ons and plugins for popular web browsers such as Mozilla Firefox or Internet Explorer that allow users to directly download videos from video portals like Youtube. These add-ons have the advantage that the videos can be downloaded directly without having to visit another website to do so.
1. Video Download Helper (Firefox): One of the most popular Firefox add-ons. It supports many different video portals including Youtube. The add-on will change its icon in the status bar whenever a website with media links is visited.
2. NetVideoHunter (Firefox):
NetVideoHunter: Will recognize Youtube videos and add them to its queue with the possibility to download the videos immediately or at a later time. Videos can also be played in the interface as well.
3. Viloader (Firefox, Internet Explorer, Opera): A plugin that installs itself in three different web browsers. It offers a download video right-click context menu option that can be used to download the videos from Youtube and other video portals.
Viloader
4. IE7Pro: IE7Pro supports Internet Explorer 8 as well despite its name. It comes with a userscript engine and a script pre-installed that can download Youtube videos. The browser plugin will display a download video link in the video description on Youtube.
5. Flash Video Downloader (Firefox, Internet Explorer, Opera): Flash Video Downloader operates a web service to download videos and an add-on that can be installed in Firefox, Internet Explorer and Opera. The Opera is one of the few Youtube video download
widgets that currently work with Opera 10.
6. Google Chrome Bookmarklet: Users can use a bookmarklet to download videos in the Google browser. All they need to do is to create a new bookmark in the web browser and add the following JavaScript code as the url:
javascript:window.location.href = 'http://youtube.com/get_video?video_id=' + swfArgs['video_id']+ "&fmt=18" + "&l=" + swfArgs['l'] + "&sk=" + swfArgs['sk'] + '&fmt_map' + swfArgs['fmt_map'] + '&t=' + swfArgs['t'];
A click on the bookmark on any Youtube video page will download that video in the Google Chrome web browser.
3ways of downloading YOU TUBE videos : 1st using Web Services
Many Internet users want to download Youtube videos. Downloading the videos can be beneficial in several ways including the option to play the video at any time without having to access the Youtube website on the Internet. It can also save bandwidth and be used to transfer the Youtube videos to devices like cell phones, media players or gaming systems that are usually not connected to the Internet or that do not offer the speed needed to enjoy the videos.
There are basically three ways of downloading Youtube videos
1. Using a web service, a web browser add-on or a standalone software program. All methods have their distinct advantages and disadvantages. Web services for example are usually independent of operating systems and can be used instantly without having to install software.They do usually lack the ability to download multiple Youtube videos at once.
2. Web browser plugins require installation. They have the advantage that they work directly on the site which is very comfortable for the user. They also usually do not provide the means to add multiple videos at once to a download queue.
3. Software programs to download Youtube videos usually come with the option to add multiple video links to the queue before starting the download. They do need to be installed on the other hand and lack a solid Youtube browser sometimes.
Online services to download Youtube videos:
Web services are websites that provide the means to download Youtube videos to a local computer system. Some offer advanced features like converting the video to another format. The list has been limited to ten free services that provide options to download Youtube videos.
1. Keepvid: A straightforward service. The user needs to paste the url of the Youtube video in the form provided on the website. Keepvid will then offer low quality and high quality downloads of the video. Works with other video portals like MySpace video or Dailymotion as well. Offers a bookmarklet which works more comfortably than copying pasting Youtube urls.
2. KCoolOnline: Currently supports 231 video portals including Youtube. It has a basic interface. All that needs to be done is to paste a video url in the form to download the Youtube video. Users who like to download videos from many different video portals might like this as it supports a lot of them.
3. Video Downloader: Another basic web interface that allows users to download and convert videos from sites like Youtube, Dailymotion or MySpace. Nothing much to say about this service except that it offers downloads in the original flv format but also in mp4 out of the box.
4. SaveVid: Offers Youtube videos in original flv or mp4 format. Displays a live list of videos that get downloaded by users on the website which can be a great source of videos as download links are displayed directly. Offers top 10 lists, archives and categories as well.
5. Video Getting: Another service that combines video downloading and conversion in one interface. Users can paste Youtube videos in the form and download them in eight different formats.
Thursday, April 15, 2010
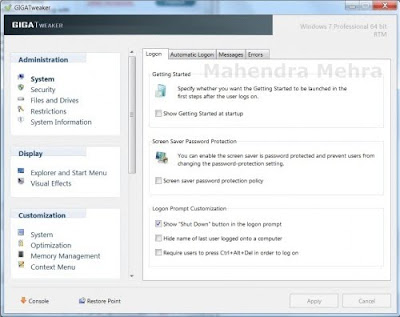
GigaTweaker : improve your windows 7 experience
GigaTweaker is a Windows 7 Tweaks software meaning it has been specifically designed for that Microsoft OS. It works with both the 32-bit and 64-bit edition of Windows 7. The tweaking software needs installation but can be used as a portable software program afterward
The interface of GigaTweaker provides access to the five main tweaking categories Administration, Display, Customization, Communication and Maintenance which all contain various subcategories like Security, Restrictions, Memory Management or Visual Effects.
- Administration: System, Security, Files and Drives, Restrictions, System Information
- Display: Explorer and Start Menu, Visual Effects
- Customization: System, Optimization, Memory Management, Context Menu
- Communication: Network, Internet Explorer
- Maintenance: Startup Manager, Uninstall Manager, Windows Utilities
Selecting a category on the left will display the tweaks that are provided on the right, often in a tabbed interface.
Most tweaks that can be applied are either self-explanatory (Disable Control Panel or Remove the shortcut arrow) or contain a short explanation what the tweak is all about.
GigaTweaker will indicate to the user if a system restart is needed to apply some of the tweaks that have been made.
There are well over one hundred tweaks available. The Windows 7 tweaker asks the user to create a system restore point on startup. Cautious users should create one to be able to return to the previous system state if something goes wrong in the tweaking session.
GigaTweaker is a portable software program for the Windows 7 operating system. It can apply lots of tweaks in Windows 7 that would take longer (and knowledge) to apply manually.
Increase your surffing speed by tweaking your browser
Settings In Microsoft Internet Explorer
- Go to "Start" and click on "Run"
- Enter "regedit" and hit "Ok" and now the Registry Editor will open
- Expand "HKEY_CURRENT_USER"
- Expand Software, Microsoft, Windows, Current Version
- Click on Internet Settings
- MaxConnectionPer1_0Server and MaxConnectionPerServer indicates the maximum number of connections per page
- Double click on one of these registries to change it. Set the radio button to DECIMAL and increase the values from default to a higher value, for example 10. Do the same with the other registry.
Settings For Mozilla Firefox
- Start Firefox and type: about:config in the address bar and hit "Enter".
- Type: network.http.pipe in the Filter search bar on top.
- Double click on the network.http.pipelining string to change its value to true.
If you use a proxy, set network.http.proxy.pipelining to true as well. - Double click on the network.http.pipelining.maxrequests string to change its integer value to 35.
- Right click anywhere on the Configuration screen and select "New" and then "Boolean".
- Enter browser.turbo.enabled as the new Boolean name and click "Ok". Now set the value of the Boolean to true
Double click on one of these registries to change it. Set the radio button to DECIMAL and increase the values from default to a higher value, for example 10. Do the same with the other registry.
Wednesday, April 14, 2010
What Are the Differences between 64-Bit and 32-Bit Processors?
To understand why 64-bit operating systems are a logical step in the evolution of the PC, consider this background information. More often than not, the maximum size of the physical memory on a computer is less than the amount needed for all running programs. This is especially true when multiple processes or applications execute simultaneously. The solution for this is that programs store some of their data on the hard drive and copy it back and forth to physical memory as needed.
This solution is often referred to as “virtual memory,” in which the computer simulates having large amounts of contiguous physical memory. A paging table is responsible for moving segments of virtual memory into physical memory as necessary. If the amount of memory demanded by all running processes exceeds the available physical memory (RAM), the paging table stores low-priority processes on the hard drive in the page file, which is much slower than RAM. When the user needs these processes, the page table re-maps them into physical memory, where the user can access them at high speeds (see Figure 1). The total number of addresses available in the virtual memory – the total amount of data the computer can keep in its working area for applications – is determined by the width of the registers on the computer processor.
Figure : The paging table moves segments of virtual memory into physical memory as needed to provide more memory to running processes.
Until recently, almost all consumer PCs used 32-bit processors. The bit size of a processor refers to the size of the address space it can reference. A 32-bit processor can reference 2^32 bytes, or 4 GB of memory. These 32-bit processors were standard at a time when 4 GB was thought to be more than enough memory space for software applications on Windows. When a process, such as running a program, is created on an x86 Windows computer with a 32-bit processor, the operating system allocates its 4 GB of virtual memory, irrespective of the actual physical memory installed on a system. Half of that allocated memory is user-accessible memory, while the other half is for kernel processes such as drivers. Modern computing systems increasingly confront the 4 GB ceiling thanks to memory-intensive applications and the need to store multiple processes in memory simultaneously.
In 2003, AMD released the first widely accepted 64-bit processor aimed at consumers, the Athlon 64, and coined AMD64 as the name for the new instruction set. Microsoft refers to the instruction set as x64, which parallels the widely accepted x86 nomenclature used for the instructions that run on most 32-bit processors.
Processors capable of referencing larger address spaces provide the opportunity to use more physical memory than ever before, potentially reducing the overhead spent moving processes in and out of physical memory. The 64-bit processors are theoretically capable of referencing 2^64 locations in memory, or 16 exabytes, which is more than 4 billion times the number of memory locations 32-bit processors can reference. However, all 64-bit versions of Microsoft operating systems currently impose a 16 TB limit on address space and allow no more than 128 GB of physical memory due to the impracticality of having 16 TB of RAM. Processes created on 64-bit versions of Windows are allotted 8 TB in virtual memory for user processes and 8 TB for kernel processes to create a virtual memory of 16 TB.
To summarize, the ability of Windows Vista and Windows 7 x64 Editions to add address more memory space than previous versions of Windows helps minimize the time spent swapping processes in and out of memory by storing more of them in RAM.
Tuesday, April 13, 2010
IN NEED OF A PROJECT OF ANY LEVEL ON ANY LANGUAGE.
CONTACT
MAHENDRA MEHRA : 9987991537
FREELANCER
QUALIFICATION : BE in INFORMATION TECHNOLOGY
COLLEGE: SPIT
check out
MAHENDRA MEHRA : 9987991537
FREELANCER
QUALIFICATION : BE in INFORMATION TECHNOLOGY
COLLEGE: SPIT
check out
some free projects
comment
Sunday, April 11, 2010
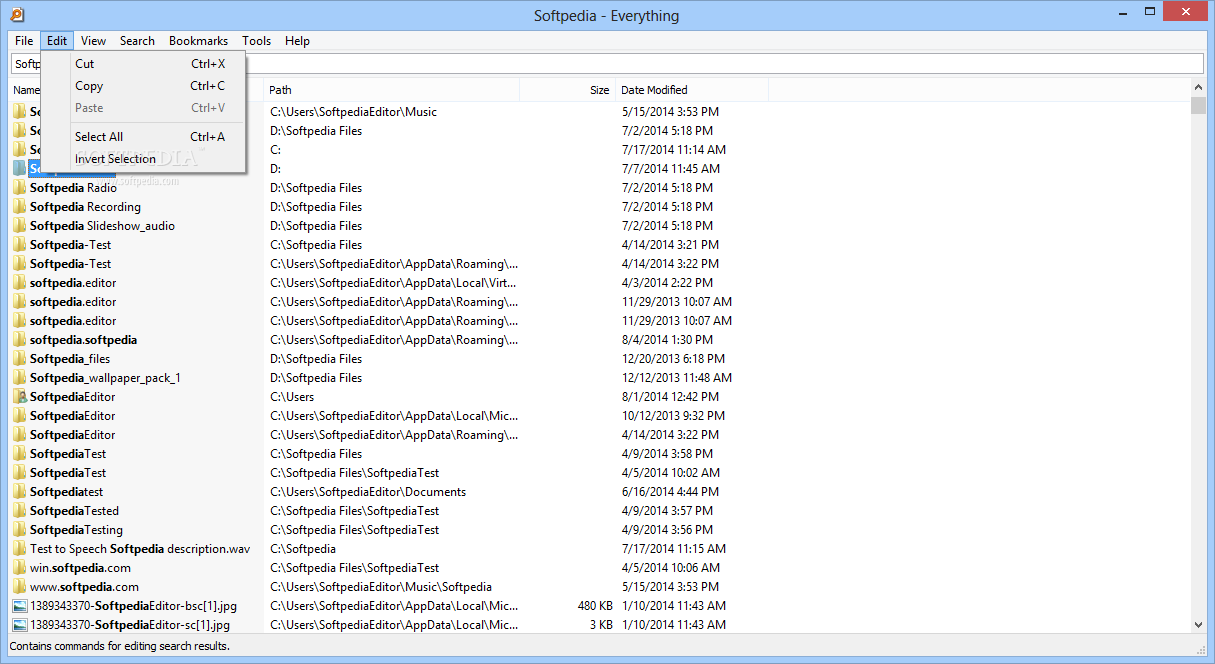
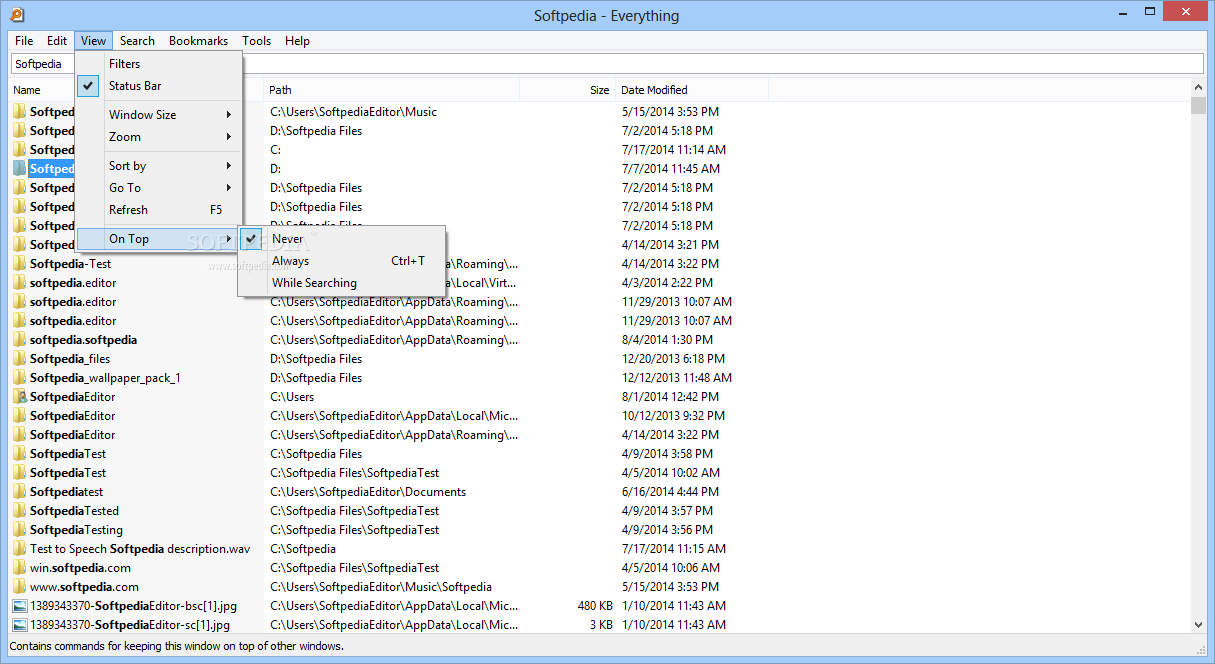
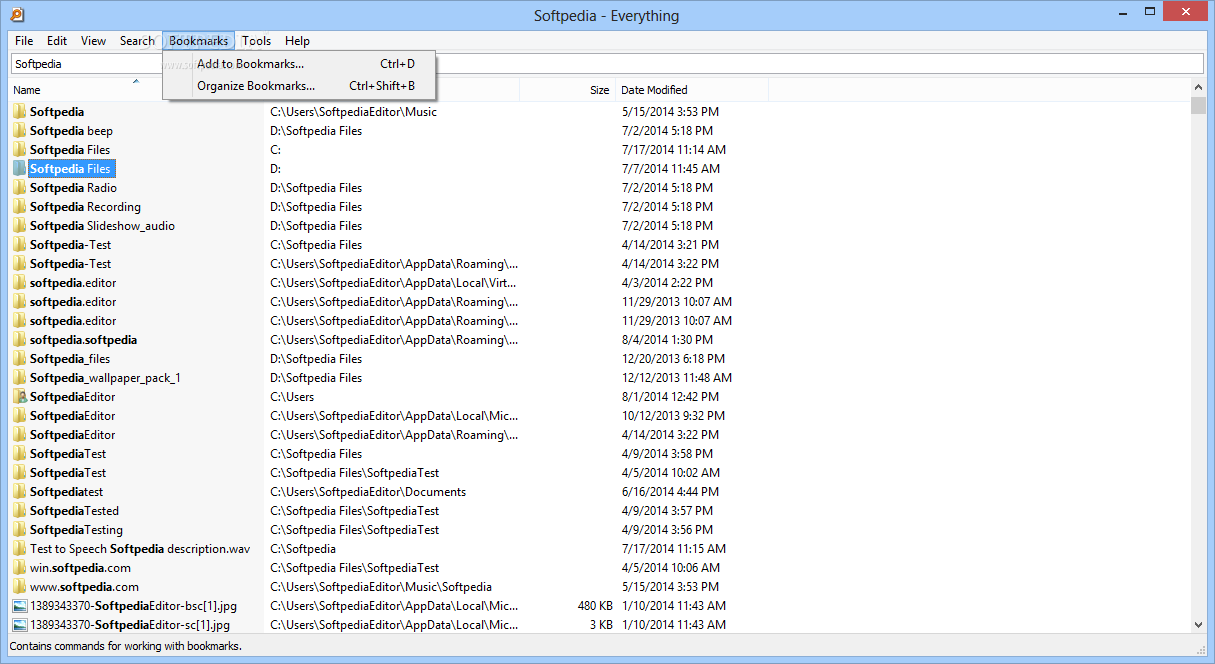
Everything: A new and 20 times faster search utility then basic search of windows
The Everything application was designed to be a fast folder and file name search engine for Windows. Unlike Windows search "Everything" initially displays every file and folder on your computer (hence the name "Everything"). You type in a search filter to limit what files and folders are displayed.
Here are some key features of "Everything":
· Small installation file
· Clean and simple user interface
· Quick file indexing
· Quick searching
· Minimal resource usage
· Share files with others easily
· Real-time updating
everything options:
we can even exclude certain location to skip the search in
Here are some key features of "Everything":
· Small installation file
· Clean and simple user interface
· Quick file indexing
· Quick searching
· Minimal resource usage
· Share files with others easily
· Real-time updating
everything options:
we can specify the drive to begin the search in
we can even exclude certain location to skip the search in
windows 7 : Shake it
Quickly minimize all other open windows in Windows 7 by shaking the only one you want displayed.
While working with multiple applications and windows in Windows 7, have you ever found the screen too cluttered? Perhaps you're mainly working in one application but want the others easily available, minimized to the taskbar.
In other versions of windows this task required a couple of steps. Right-click the taskbar and minimize all windows, then click on the taskbar button representing the window you want remaining open. But in Windows 7 there's another way...
Left-click on the title bar of the window you want remaining open and keep the mouse button help down. Now "shake" your mouse pointer quickly and the other windows will minimize to the taskbar, keeping the shaking window open.
before
after shaking the notepad , it remains active on screen rest others are minimized to the task bar
While working with multiple applications and windows in Windows 7, have you ever found the screen too cluttered? Perhaps you're mainly working in one application but want the others easily available, minimized to the taskbar.
In other versions of windows this task required a couple of steps. Right-click the taskbar and minimize all windows, then click on the taskbar button representing the window you want remaining open. But in Windows 7 there's another way...
Left-click on the title bar of the window you want remaining open and keep the mouse button help down. Now "shake" your mouse pointer quickly and the other windows will minimize to the taskbar, keeping the shaking window open.
before
after shaking the notepad , it remains active on screen rest others are minimized to the task bar
Subscribe to:
Posts (Atom)